Distributed Key Topologies
EncrypTight User Guide 19
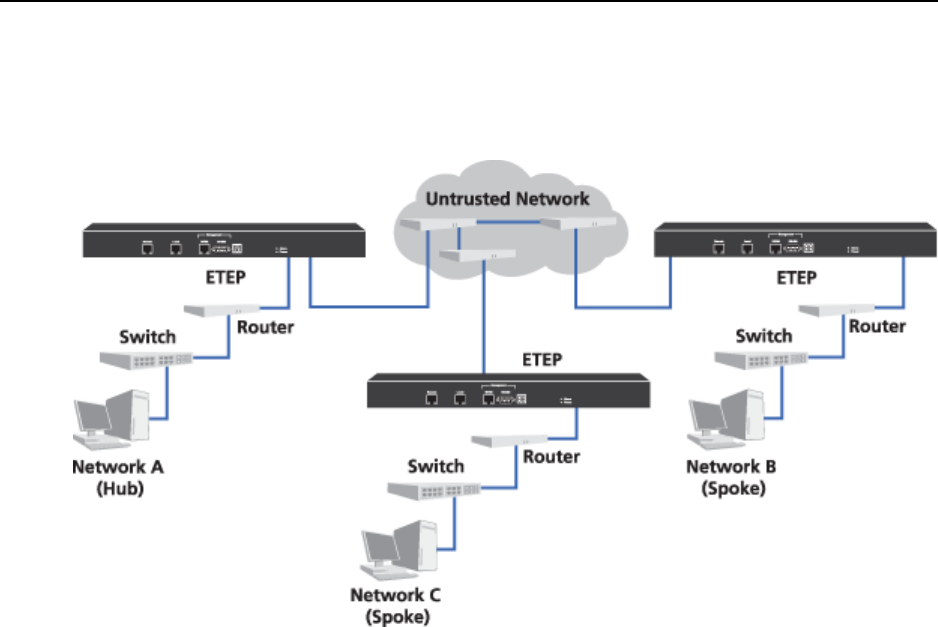
Regardless of topology, PEPs are typically located at the point in the network where traffic is being sent
to an untrusted network or coming from an untrusted network. As an example, Figure 2 shows a hub and
spoke network secured with EncrypTight.
Figure 2 PEPs in a Hub and Spoke network
PEP A encrypts data traffic from Network A that goes to Networks B or C. PEP A also decrypts data that
originates from Networks B and C. PEP B encrypts data from Network B that goes to Network A and
decrypts data that comes from Network A. PEP C encrypts data from Network C that goes to Network A
and decrypts data that comes from Network A.
Related topics:
● “EncrypTight Element Management System” on page 20
● “Policy Manager” on page 20
● “Key Management System” on page 20
● “Policy Enforcement Point” on page 21
EncrypTight Elements
EncrypTight consists of a suite of tools that perform various tasks of appliance and policy management:
● EncrypTight Element Management System is the element management component of the EncrypTight
software
● Policy Manager is the policy generation and management tool
● Key Management System is the key generation and distribution tool
● Policy Enforcement Points are the encryption appliances that enforce the security policies
The number of ETEPs that you can manage and the speed at which they run is controlled by licenses.
You must enter a license for EncrypTight before you can install licenses on the ETEPs.