Adding Layer 3 IP Policies
EncrypTight User Guide 205
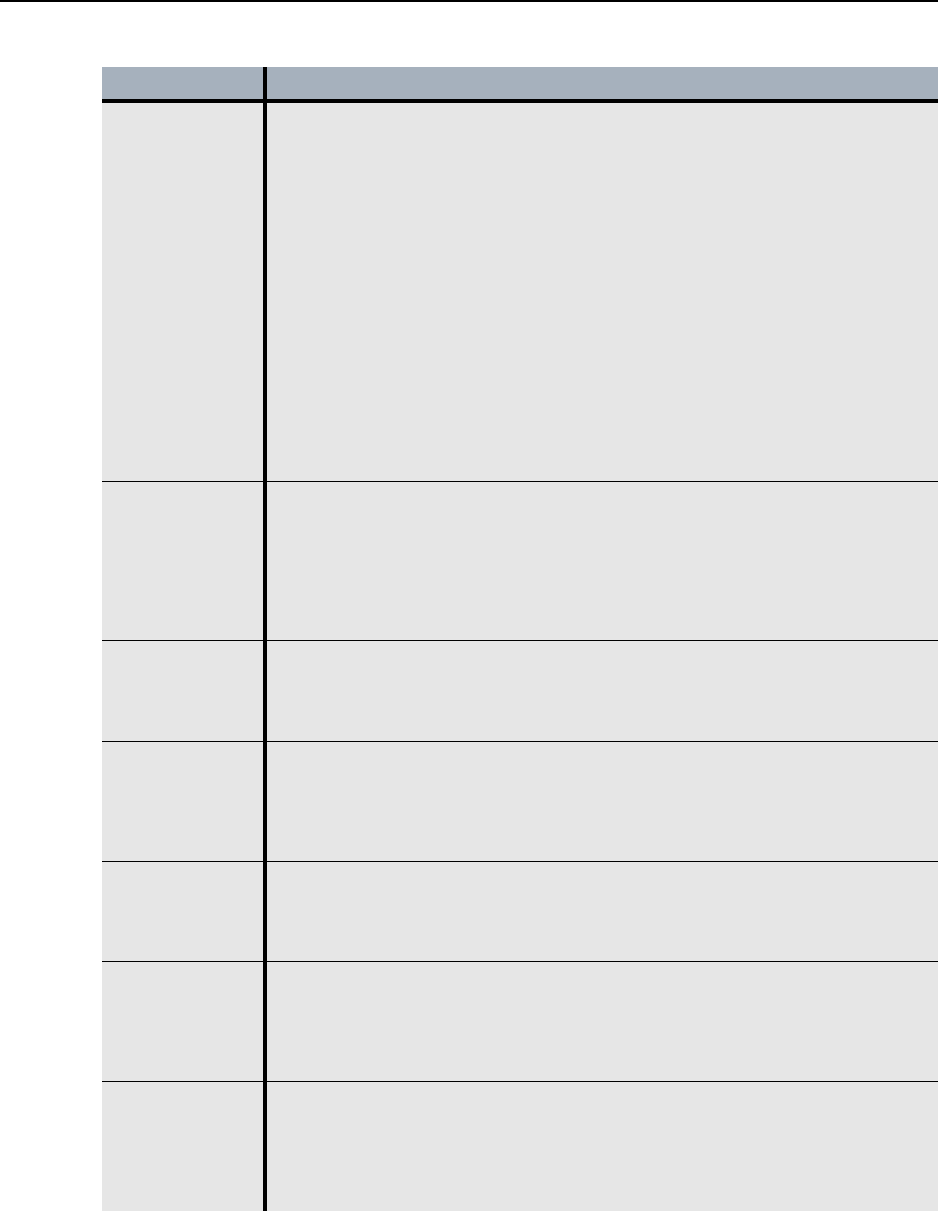
Addressing
Mode Override
Overrides the Network addressing setting for the network sets.
• Preserve internal network addresses - This setting overrides the network
set’s network addressing mode and preserves the network addressing of the
protected networks. The IP header contains the source address of the
originating network.
If this setting is disabled and the addressing mode of the network set uses
the PEP’s remote IP address or a Virtual IP address, the IP header contains
the source address as specified in the network set. If the addressing mode
of the network set preserves the network IP address, disabling this setting
has no effect.
• Preserve address, protocol and port - This setting overrides the network
set’s addressing mode and preserves the network addressing of the
protected networks, as well as the specified protocol and port numbers. The
IP header includes the source address, protocol, and port of the originating
network. This allows you to send the Layer 4 header information in the clear
for traffic engineering and Service Level Agreement (SLA) management (for
example, Quality of Service controls).
Minimize Policy
Size
Reduces policy size by ignoring the network addresses on the local port of the
PEP. This reduces the amount of network traffic needed to renew keys and
refresh policy lifetimes.
• Minimize Policy Size (Ignore Source IP) - This setting replaces the source
network address for outbound traffic and the destination network address for
inbound traffic with all networks wildcard addresses (0.0.0.0/0). For more
information, see “Minimizing Policy Size” on page 187.
Point A -
Network Set
Identifies the network set included in this policy for one side of the point-to-point
network configuration.
• Click the Network Sets tab of the EncrypTight Components view and drag
the appropriate network set to the Point A - Network Set.
Point A - Ports Specifies the source and destination ports for the network set selected for Point
A. In TCP and UDP, port numbers are used to identify well-known services,
such as FTP, e-mail and so on. Choosing a specific port limits the action of the
policy to traffic using that port.
This setting is only valid if the protocol is set to 6 (TCP) or 17 (UDP).
Point B -
Network Set
Identifies the network set included in this policy for the other side of the point-
to-point network configuration.
• Click on the Network Sets tab of the EncrypTight Components view and
drag the appropriate network set to the Point B - Network Set menu.
Point B - Ports Specifies the source and destination ports for the network set selected for Point
B. In TCP and UDP, port numbers are used to identify well-known services,
such as FTP, e-mail and so on. Choosing a specific port limits the action of the
policy to traffic using that port.
This setting is only valid if the protocol is set to 6 (TCP) or 17 (UDP).
Protocol Specifies the Layer 3 protocol affected by this policy. The action selected for
the policy is only applied to the traffic with the specified protocol.
•Any - specifies all protocols
•Only - specifies a particular protocol. Click to select and then enter the
required protocol in the range 0 to 255.
Table 51 Point-to-point policy entries (continued)
Field Description


















